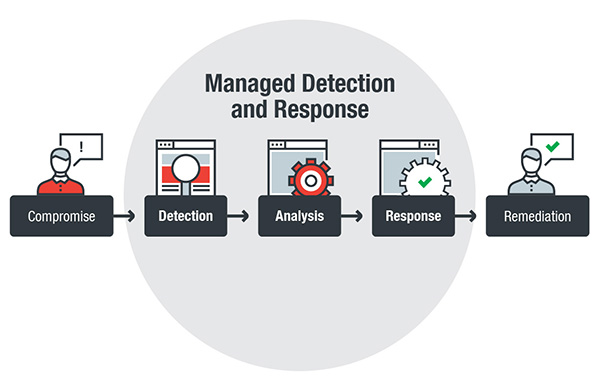
Handled detection and also reaction makes it possible for a positive technique to security with its ability to identify as well as totally assess risks and also immediately respond to incidents. With the range as well as complexity these days’s dangers– whether cyberespionage- or cybercrime-driven– the risks are high. Organizations identify this: international costs on cybersecurity has raised, driven by regulatory conformity and the requirement to develop or boost discovery and reaction abilities.
Here’s a closer look at the challenges that enterprises deal with when taking on an extra durable cybersecurity strategy:
TODAY’S RISKS ARE BYPASSING TRADITIONAL SAFETY DEFENSES.
Typical protection solutions, which often tend to reply to dangers reactively and also supply surveillance of just a solitary vector, are no longer enough versus the wide range of risks in the existing danger landscape. In the very first half of 2018, Fad Micro obstructed over 20.4 billion threats. Cryptocurrency-mining malware, for example, rose by 141 percent. Some current hazards have actually also showed aggressors incorporating the capabilities, evasion methods, and also perseverance mechanisms of various malware tools. Amongst them: adding file encryption to banking trojans and cryptocurrency-mining malware, lying inactive, and using other devices– routers, printers, scanners, and various other internet-of-things gadgets– to acquire a grip on the system or server.
The SANS Institute reported that actively hunting risks– which includes iteratively finding as well as examining risks and invasions– can measurably enhance details safety programs as well as rate and precision in incident response, at least for huge enterprises.
Nevertheless, several organizations may not have the sources or capacity to proactively hunt threats. Running a safety and security operations center (SOC), for instance, or using endpoint discovery as well as reaction (EDR) tools, call for know-how.
Also if a huge organization has the funds to establish an SOC or buy protection devices, it doesn’t always convert to efficient details security and danger monitoring.
How can MDR address this difficulty?
MDR gives companies the security needed to ward off not only evasive threats, however their related activities such as establishing command-and-control (C&C) communications, side motion, and also evasion methods that can bypass basic safety defenses.
MDR offers danger searching services across the organization’s environments, sweeping for indications of compromise or attack to better combat comparable risks. MDR also enables organizations to leverage a safety and security carrier’s extensive research study and danger intelligence that can offer context and workable understandings into an attack– to ensure that companies can quickly determine and also react to it.
An excellent MDR provider must have the capacity to assess details of system and also network-based behaviors as well as events (both in bit and also individual levels) as well as network metadata that organizations can access as well as track to much better comprehend a threat’s kill chain.
CYBERSECURITY SKILLS GAP REVEALS ORGANIZATIONS TO RISKS.
Many companies take on brand-new or extra technologies to support their development. For hazard actors, this suggests more doorways to a company’s delicate and mission-critical information. Dangers can impact organizations in manner ins which can be testing to anticipate.
There is a difference in what enterprises require and also the staff they really have. This void is progressively broadening: It’s estimated that by 2022, there will be 1.8 million open positions in cybersecurity. And also in spite of digital protection being a concern, just 65 percent of evaluated companies had a real professional to tackle their cybersecurity. This is specifically real for enterprises whose size can not validate the costs of employing devoted cybersecurity professionals.
The apparently overwhelming tasks of protecting a business can place a stress on IT staff, which typically additionally handle day-to-day procedures– monitoring and also maintaining networks, web servers, as well as systems up as well as running.
For business utilizing EDR solutions, the difficulty depends on being able to totally make best use of or effectively make use of these tools. They need the abilities to do so. As well as while sophisticated safety and security solutions such as machine learning-based remedies and EDR innovations aid, they are not silver bullets. They are just as efficient as individuals that use them.
Just how does MDR resolve this obstacle?
MDR provides an appropriate combination of people, procedure, as well as modern technology. MDR addresses the difficulties in workforce and expenses entailed by offering on-demand access to full-time hazard experts, detectives, and occurrence action professionals.
Safety notifies, logs, and information, by themselves, do not really give context. They may inform regarding a safety case, but it is up to the company as well as its protection team to understand them, figure out what happened, and determine what to do about it. MDR relieves the concern of risk hunting, examination, and also correlation, log aggregation, sharp triage, and also safety information evaluation. A great MDR company is able to do continual occasion monitoring and alerting and also check out occasions or events once they are verified.
There must be routine solution testimonials that recognize considerable events and cases and help make improvements exactly how discovery and also response abilities are released. This can consist of partnership between the MDR supplier and customer in regards to reviewing a network packet captured from a firewall or invasion discovery and also prevention system, for instance, or determining the entry point a fileless cryptocurrency-mining malware made use of to get into the servers.
ALERT EXHAUSTION CAN LEAD ORGANIZATIONS TO NEGLECT INVASIONS.
A.
security alert might alert concerning discovery of malware on an endpoint, but it may not define if it originated from an exploit, spam e-mail, or harmful site, if it was injected on a system procedure, or if it has currently spread across systems attached to an afflicted network.
Verifying signals can take a substantial amount of time and resources; as well as teams may wind up prioritizing the wrong informs, running after incorrect positives, or filtering through repetitive alerts across various safety and security devices.
With the high quantity of alerts, it can be challenging to identify which needs to get prioritized and also swiftly addressed. For instance, 37 percent of surveyed bank safety principals kept in mind that their banks process over 200,000 protection informs each day. A recent study additionally noted that 79 percent of cybersecurity personnel really feel flooded by the quantity of security notifies, and also the workload of handling vulnerabilities in their IT facilities.
The relevance of alleviating alert tiredness is exemplified by the data violation at Target, where cyberpunks swiped 70 million credit card records. While the case seemed alarms, they were neglected for months as its safety team was receiving similar notices that turned out to be false positives. The effect: US$ 292 million in financial losses.
Exactly how does MDR resolve this obstacle?
MDR alleviates alert exhaustion by correlating countless signals, determining what needs to get focused on and also addressed.
MDR offers innovative risk connection, which evaluates risk information from endpoints and networks to repaint a more clear photo of an assault: where it came from, just how it spread out, and if it already influenced the network and also systems attached to it. Validated danger signals shouldn’t come as basic notices, either. A great MDR company furnishes event cases that consist of indicators of compromise or attack, impacted hosts, and also recommended reduction methods.
A tangible example of this is MDR’s automated hazard correlation establishing if an alert that appears fairly benign is actually component of a bigger strike. It can minimize the “dwell time” of threats, by establishing if a tool (i.e., printers as well as scanners) that doesn’t typically have safety systems in position is contaminated with malware or is showing strange behavior.
By maximizing resources set aside to taking care of alerts, an organization’s IT or safety team can focus on what issues most– mitigating risks and rapidly reacting to hazards.
TOOK CARE OF DETECTION As Well As FEEDBACK AIDS BRIDGE CYBERSECURITY SPACES.
Organizations emulate challenges that can threaten the effectiveness of their safety position: the raising refinement of threats and also complexities in handling the IT framework, a scarcity in cybersecurity skill, and inundation of safety signals. Handled discovery and action helps by connecting spaces in an enterprise’s cybersecurity pose through a comprehensive innovation stack managed by devoted researchers and also analysts.